 Why the big focus on technical security solutions is like a sound bite!
Why the big focus on technical security solutions is like a sound bite!
Here we are at the primary season preceding the 2016 Presidential elections after a “sound bite summer” about ISIS, immigration, Greece, an email server and of course, ‘The Donald.' Yet the reality is that most elections are won and lost on the state of the economy.
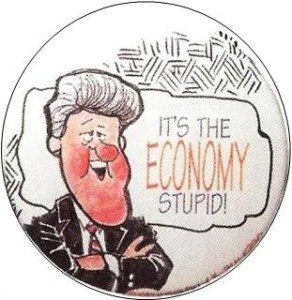
As the Bill Clinton 1992 Presidential key campaign slogan went, “It’s the economy, stupid.” When it comes to data breaches, we could coin a similar slogan, “It’s the people, stupid!”
Despite evidence that most data breaches are rooted in employee negligence, not a technical security failure, most solutions continue to be technical. Prime example: After the Anthem breach announcement, New Jersey mandated that health insurance carriers encrypt all personal data. But the Anthem breach was a credentials violation, meaning the hackers obtained user IDs and passwords. Encryption wouldn’t have helped. Executives, similar to politicians, probably prefer to go with the sound bite, particularly one with what looks like a plug and play solution. Who wouldn’t? Add encryption and more sophisticated log monitoring; beef up perimeter security and so forth, and voila! Checklist complete. It is highly preferable over digging into the (broad and time-consuming) people side of the security risk, right?
Employee Negligence: Phishing Scams, Stolen Devices, and File Sharing
In 4 Reasons why Healthcare Data Breaches will continue to rise, we mention that the greater number of people who have access to personal health data, the greater the data security risk. Technical security can’t prevent human error. Remember that while the Anthem breach was a sophisticated phishing scam, it still required people to click on a link from a fake email. According to the 2015 Verizon Data Breach Report, almost 25% of recipients will open a phishing message, half of them within an hour of receiving the message! In more sophisticated phishing campaigns where the individual receives a series of scam emails, the open rate is as high as 90%. What’s more, the Ponemon Fifth Annual Privacy and Security of Healthcare Data Report cites employee negligence as the single largest concern for health care organizations, with lost or stolen devices and phishing attacks happening far more frequently than any other type of incident, including cyber-attacks – and that’s not even touching on unsecured file-sharing.
So why is it that even as healthcare data breach incidents continue to rise, healthcare organization IT budgets only spend an average of 3% on Information Security? Maybe because the focus remains on the technical vs. the people, policies, and procedures. The same Ponemon report says that more than 42% of healthcare organizations and 50% of Business Associates self-report that they do not have sufficient policies and procedures in place.
Unfortunately, technical band-aids won’t solve security breaches, much like sound bites couldn’t fix the economy. Instead, you need a “We the people” approach, because regulatory compliance and effective security start with an organization’s people – all of its people. Not only the IT department or the Compliance team. With proper training on correct procedures, strong policy development and continual tracking, healthcare organizations can go a long way toward preventing a data breach.
To learn more about IT Security and Compliance and how your company measures up on best practices, take a free online High-Level Assessment.
[/av_textblock]

September 14, 2015

Comments