Security certifications are fast becoming need-to-haves for vendors and technology firms.
Certifications, such as SOC 2, can offer a cost-efficient way of demonstrating effective risk management practices and meeting regulatory compliance directives.
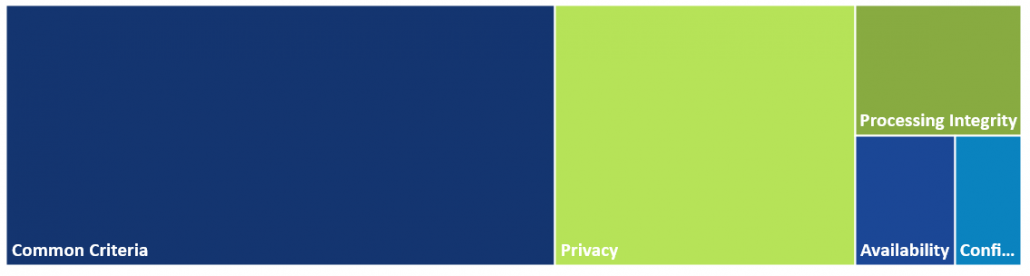
In the case of SOC 2 reports, you’re focusing on non-financial reporting controls that are based on five Trust Service Principles: Common Criteria, Availability, Processing Integrity, Confidentiality, and Privacy. You can choose to report on any of the Trust Service Principals, but you must include Security as it's part of the Common Criteria. Adding additional principles increases the scope of criteria which makes the reports more expensive and more time-intensive. When selecting your Trust Service Principles, keep in mind that your auditor or preparer can suggest and make recommendations about which ones to include, but ultimately the decision is made by the management team of your organization.
The pathway to SOC 2 reports, whether Type I or Type II, takes significant preparation. Type I is a “point in time” report on your system and processes, whereas Type II looks at a minimum of 6 months of evidence and is much more comprehensive. Type II provides more assurance as the auditor tests the operating effectiveness of the controls. Both require that you demonstrate a mature security program.
Pre-Audit Preparation
Deciding on your SOC 2 reporting period is crucial when scoping out your report. Make sure you narrow down on the systems which you do want in scope. We recommend choosing systems that contain sensitive data such as Protected Health Information (PHI). Your service organization should only report on what is relevant to the user entities. We also recommend completing a gap analysis to verify that all key controls are documented and in place. After you've completed your gap analysis, ensure that you leave yourself enough time for remediation.
Many organizations don't do all 5 Trust Services Principles in one report - especially at the beginning. You can build upon a SOC 2 report as your security program matures. You can save significant time and resources just by getting your ducks in a row before diving into a SOC 2 audit. With the supportive platform of Ostendio’s MyVCM and its partner CPA firms and compliance experts, your SOC 2 audit and certification preparation become very doable.
Collection of Evidence
When it comes to SOC 2, if you didn’t document it, it didn’t happen. Examples of evidence include organizational charts, asset inventories, evidence of on-boarding and off-boarding processes, and change management. When reviewing the evidence, the auditor may choose to conduct on-site interviews or complete them by phone. The report can take between 6 – 8 weeks for small companies, or several months for larger companies – depending on the scope of the report.
SOC 3 Reports
A SOC 2 report contains sensitive information about your company's processes and controls. We recommend only sharing your SOC 2 report once an NDA has been signed. An alternative option would be to complete a SOC 3 report instead - which is a general use report. The main difference between a SOC 3 and SOC 2 report is that the SOC 3 only provides an opinion letter, system description, and potentially a SysTrust Seal (for unqualified opinions only).
MyVCM gives you all the tools you need to prepare for SOC 2 activities.
• Single platform management for information security, privacy, and compliance activities
• Supports your ability to assess and identify vulnerabilities and compliance gaps
• Comes with policy and procedure templates, asset inventory tracking, and management tools
• Provides document management and learning tools that support your security and privacy framework build-out and ongoing administration
• Built-in dashboard and reporting tools that let you quickly and efficiently share how responsibly your compliance program operates with clients, partners - and auditors!
Successful SOC 2 audit results are rooted in readiness.

March 19, 2018
Comments